Zero Trust for Cloud Workloads Starts With Identity, Not the Network
Most cloud breaches no longer begin with someone “breaking through the perimeter.” They begin with a token, a role, a service account, or a workload identity that already has the right to be there. That is why zero trust in the cloud has to start with identity governance for workloads, not with another layer of network controls. If your containers, functions, CI/CD runners, and automation accounts can quietly accumulate standing privilege, your network is not your primary security boundary anymore.
Security teams know this in theory, but many cloud programs still roll out zero trust in the wrong order. They spend months on segmentation, private connectivity, and policy engines while service principals, managed identities, IAM roles, and service accounts remain under-owned and under-monitored. The result is a modern-looking architecture with a familiar old weakness: too much trust in machine identities. A more practical program starts by tightening how workloads authenticate, what they can access, how long that access lasts, and how you prove it is being used correctly.
Why identity is the real control plane in cloud environments
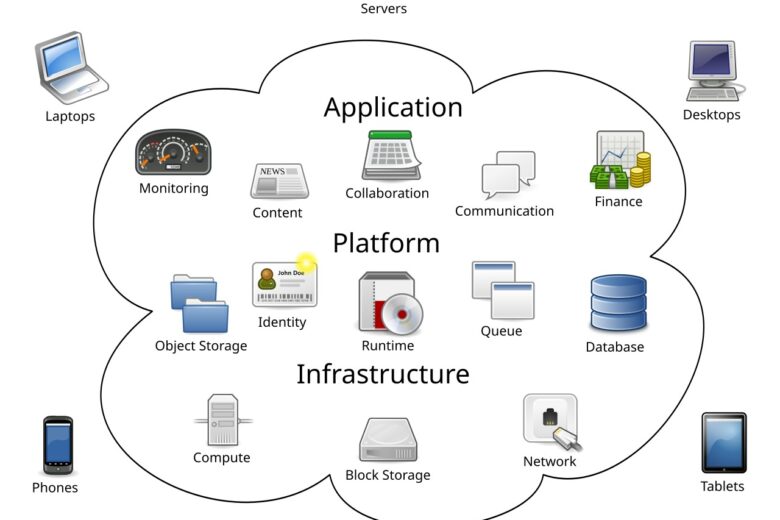
NIST’s zero trust architecture guidance is still the cleanest framing here: protect resources, not network segments, and make authentication and authorization explicit before a session is established. In cloud platforms, that principle lands squarely on identity. Workloads talk to APIs, object stores, databases, queues, secret managers, and control planes through identities. If those identities are weakly governed, broad, or long-lived, attackers do not need east-west network freedom to do serious damage.
CISA’s Zero Trust Maturity Model reinforces the same shift. Zero trust is about granular, per-request access decisions and the visibility required to evolve policy over time. That matters because cloud workloads are dynamic. Pods scale up and down, serverless functions appear for seconds, CI jobs run in external platforms, and third-party SaaS integrations ask for standing permissions that no one reviews after onboarding. The old habit of saying “it runs inside our environment, so it is trusted” simply does not survive contact with cloud reality.
The strongest architectural signal from the major cloud providers is also consistent: AWS recommends temporary credentials with IAM roles; Google advises avoiding service account keys whenever possible; Microsoft positions managed identities specifically to reduce credential handling. Those are not cosmetic best practices. They are admissions that long-lived workload credentials are one of the most dangerous forms of hidden trust in cloud systems.
The failure modes that break zero trust programs in practice
Most organizations do not fail because they lack a zero trust strategy deck. They fail because workload identity sprawl grows faster than control maturity. These are the patterns that show up again and again:
- Long-lived secrets in pipelines and apps. Service account keys, client secrets, or access tokens end up in CI variables, parameter stores, desktop notes, or old deployment scripts. They stay valid far longer than anyone intended.
- Broad roles for convenience. Teams give a workload “temporary” admin-like access to unblock delivery, then never come back to reduce scope.
- No owner for machine identities. Human accounts usually have HR-backed lifecycle management. Workload identities often do not. Nobody can answer who owns them, whether they are still needed, or what business process depends on them.
- Poor provenance for external workloads. GitHub Actions, third-party scanners, SaaS connectors, and cross-cloud integrations often authenticate into the environment with weak attestation or over-permissive trust policies.
- Weak telemetry. Logs show that a role or service principal acted, but not whether that use was expected, unusual, or materially risky.
- Static exceptions. Break-glass roles and migration exceptions stay in place indefinitely and quietly become the normal operating model.
This is why “identity-first zero trust” is not just a slogan. It is a sequencing choice. If these issues remain open, network controls mostly slow down the easier attacks while leaving high-value trust paths intact.
A practical target architecture for identity-first zero trust
A workable design does not need to be exotic. It needs to be opinionated. Start with the assumption that every workload must present a verifiable identity, receive only narrowly scoped authorization, use short-lived credentials by default, and generate auditable activity that can be linked to a system owner and business purpose.
In practice, that architecture usually looks like this:
- Platform-native workload identity first. Use IAM roles on AWS, managed identities on Azure, and Workload Identity Federation or attached service accounts on Google Cloud before considering static keys.
- Federation for external compute. If a workload runs outside the target cloud, prefer OIDC, SAML, X.509-backed federation, or equivalent temporary credential flows instead of exported keys.
- Policy at the resource edge. Enforce access at APIs, data services, secret managers, and control planes. Network location can complement policy, but should not substitute for it.
- Attribute-aware authorization. Bind access to workload type, environment, repository, namespace, cluster, account, region, or deployment stage where the platform supports it.
- Central inventory and ownership metadata. Every machine identity should have an owner, purpose, environment tag, creation date, and expected usage pattern.
- Detection tied to misuse patterns. Alert on impossible geography for control-plane use, unusual token issuance volume, role assumption from new contexts, dormant identities becoming active, and privilege paths that were never exercised before.
Notice what this architecture avoids: a fantasy in which everything is solved by microsegmentation. Segmentation still matters, especially for blast-radius reduction and legacy systems, but it should be layered behind identity assurance rather than treated as the core trust decision.
What to control first: the five highest-value moves
If the program is early or uneven, these five moves usually deliver the fastest security lift:
- Eliminate long-lived workload credentials wherever you can. Start with cloud-native workloads and CI/CD. Replace embedded keys with role attachment, managed identity, or federation. This single move reduces theft risk, rotation debt, and accidental credential reuse.
- Build a workload identity inventory. Include service accounts, managed identities, roles, service principals, automation users, and third-party connectors. Add owner, purpose, last used date, privilege level, and credential type.
- Cut broad permissions based on observed use. Use access analysis and actual call history to right-size permissions. This is where providers give you leverage: IAM analysis on AWS, policy recommendations and sign-in data in Azure, and policy intelligence in Google Cloud.
- Put external runners on stronger trust rails. For GitHub Actions and similar systems, require OIDC-based federation with strict audience, subject, repository, branch, and environment conditions when supported.
- Instrument anomaly detection around machine identities. It is not enough to log issuance and use. You need detections tuned to workload abuse, not just human login abuse.
These controls are actionable because they reduce both likelihood and blast radius. They also create the visibility needed for the next layer of maturity.
How to roll this out without breaking engineering teams
The mistake many security teams make is trying to “clean up identity” as a one-time hardening exercise. That usually creates friction, emergency exemptions, and rollback pressure. A better rollout is phased and evidence-driven.
Phase 1: Discover and classify
Inventory all workload identities and sort them by environment, privilege, credential type, owner quality, and internet exposure. Flag the worst combinations first: high privilege plus static credential, external compute plus standing secret, dormant identity plus powerful access.
Phase 2: Migrate the easy wins
Target workloads already running on native cloud compute. Migrating them to attached roles or managed identities is usually lower-friction than redesigning third-party integrations. Pair each migration with a permission review so you do not simply preserve old overreach in a new mechanism.
Phase 3: Fix CI/CD and cross-boundary trust
This is where many real attack paths sit. Replace exported credentials in pipelines with federation. Narrow trust relationships by repo, branch, workflow, environment, and issuer. Validate that artifact signing, deployment attestations, or equivalent provenance signals are available where the platform supports them.
Phase 4: Add preventive guardrails
Prevent new static credentials unless a documented exception is approved. Block creation of overbroad roles without justification. Require tags and ownership metadata for new workload identities. Make the secure path the default path.
Phase 5: Optimize with telemetry and review loops
Review unused permissions, dormant identities, and exception age monthly. Mature programs treat workload identity governance as an operating rhythm, not a project with an end date.
Metrics that actually tell you whether the program is working
Security teams often report the wrong numbers here. “Number of policies reviewed” is activity, not progress. Better metrics show risk reduction and operational fit:
- Percentage of workloads using short-lived credentials
- Percentage of machine identities with a verified owner
- Count of static service account keys or client secrets by environment
- Median privilege reduction after policy right-sizing
- Percentage of external CI/CD trust paths using federation instead of stored secrets
- Mean time to revoke or rotate compromised machine credentials
- Number of dormant machine identities removed per month
- Alert precision for machine-identity misuse detections
A useful benchmark is not perfection on day one. It is clear directional change. If the count of long-lived credentials is flat, ownership coverage is poor, and exceptions keep growing, the zero trust program is not actually moving the trust boundary.
Common objections from engineering and how to answer them
“This will slow delivery.”
Only if the secure pattern is harder than the insecure one. Provide templates, modules, and documented examples so teams can adopt native workload identity without inventing it from scratch every time.
“Some third-party tools still need secrets.”
True. Zero trust is not denial of reality. Track those exceptions, shorten their lifetime, scope them narrowly, and make replacement part of vendor governance.
“We already have network controls.”
Good. Keep them. But recognize what they cannot do. They do not make a stolen token less valid, and they do not fix an overprivileged role that is being used exactly as configured.
“The cloud provider already secures this.”
The provider secures the platform. You still own who gets to act inside your tenant, project, or account, and under what conditions.
An actionable checklist for the next 30 days
- Export a full inventory of service accounts, managed identities, IAM roles, service principals, and automation identities.
- Mark which ones use static credentials and which use ephemeral or federated access.
- Identify the top 20 most privileged machine identities and verify business owner plus last use.
- Replace at least one high-volume CI/CD secret flow with OIDC or equivalent federation.
- Enable or review provider-native access analysis to identify unused permissions.
- Create a policy that new workload identities require owner, purpose, environment, and expiration or review date.
- Write at least three detections specific to machine identity abuse, not just user sign-in abuse.
- Review break-glass and migration exceptions and assign removal dates.
If a team can do only a few things this quarter, do these. They change the practical trust model much faster than debating abstract maturity levels.
FAQ
Is zero trust just identity and access management?
No. Network controls, device trust, data protections, monitoring, and application security still matter. But in cloud workloads, identity is usually the first control point that determines whether access happens at all.
Do service accounts always need to be removed?
No. They often remain necessary. The goal is to manage them as sensitive resources, reduce standing privilege, avoid exported keys, and maintain strong ownership and telemetry.
What is the biggest mistake in cloud zero trust programs?
Starting with architecture diagrams and segmentation while ignoring long-lived machine credentials and overprivileged workload identities already active in production.
How do you handle legacy systems that cannot use federation?
Treat them as controlled exceptions. Scope access tightly, isolate them as much as possible, rotate secrets aggressively, monitor every use, and put migration off the exception list only when there is a real plan and date.
What does “identity-first” look like in a multi-cloud environment?
Use the strongest native workload identity model in each cloud, normalize inventory and ownership centrally, and set common policy goals: short-lived credentials, verified provenance, least privilege, and detectable misuse.
Final take
Zero trust in cloud security becomes real when you stop treating the network as the main arbiter of trust and start governing machine identities with the same seriousness you apply to human admins. The hard part is not understanding the principle. The hard part is removing convenience-based trust from real systems without breaking delivery. That is exactly why workload identity should be the first serious battleground. If you get that layer right, the rest of the zero trust stack has something solid to stand on.